Exchange Online Protection (EOP) is an email filtering service that allows you to control your organization’s anti-spam and email management settings. EOP provides malware filters, connection filters, content filters, outbound spam, and quarantine lists centered on the requirements of your organization.
EOP is an average\good SPAM\Malware filtering service. It has gotten much better over the last two years and continues to improve. For large organizations, my recommendation is to use a 3rd party cloud-base SPAM\Malware provider in conjunction with EOP, or buy the add-on Advance Threat Protection (ATP) (part of E5 or $2 per mailbox) to add another layer of protection. ATP isn’t the highest rated gateway solution in Gartner reports, however, it is among the top tier.
More information on ATP can be found here.
Before you rush out and spend money on a new service, I’ve put together my thoughts and experiences with EOP and Office 365. Sometimes a few tweaks can help reduce the amount of SPAM messages you’re receiving.
Email Validation
SPF
The SPF record is configured to specify which computers are authorized to transmit email from your domain. SPF records help to prevent others from using your domain to send spam or other malicious email. As more email environments query for SMTP domain SPF records, you must create or modify your SPF records to allow Exchange Online to send email from your domain successfully.
EOP can validate inbound email messages are being sent from a verified IP address that matches the sending domain. If the sending IP address does not match the SPF record of the sending domain, EOP can hard fail the message. Many organizations are moving to rejecting email messages that fail the SPF check.
DKIM
You can find background information regarding DKIM from this article. You should use DKIM in addition to SPF and DMARC to help prevent spoofers from sending messages that look like they originated from your domain. DKIM lets you add a digital signature to email messages in the message header. I know this sounds complicated, but it’s not. When you configure DKIM, you authorize your domain to associate, or sign, its name to an email message by using cryptographic authentication. Email systems that receive email from your domain can use this digital signature to help determine if incoming email is legitimate.

Malware Filter
The default malware filter does a good job at blocking most Malware, and its configuration is fairly straight forward. All messages transported through Office 365 are scanned for malware. If malware is detected, it is deleted. Options within the malware rules include blocking file extensions and notifying any relevant parties that malware has been detected.
The challenge with all malware filters is the unknown, or any new malware. Messages with new malware could potentially pass through your malware filter because the malware engines either haven’t been updated with the latest signature, or the malware hasn’t made it to the block list. Although possible, this scenario is very uncommon.
It is always good, however, to have an action plan in the event that malware makes it through your filter. If this scenario were to occur, first you need to block any new messages with malware by setting up a transport rule. Secondly, find and destroy any email messages that contain malware.
This article provides guidance on how to find and destroy SPAM\malware email messages.
This article provides advice on how to create a transport rule based on attachment type.
File Extension
EOP also has an attachment blocking capability. By default, the list below provides the attachment extensions that are blocked:

I recommend enabling the file extension block. If you have a user base that should be an exception to the rule, you can simply create a new malware filter.
https://technet.microsoft.com/en-us/library/jj200669(EXCHG.150).aspx
Notification
At a minimum, administrators should be notified when email messages with malware or restricted file types are deleted.
Some organizations want VIPs to be alerted when an email message is deleted because a blocked file type is detected. In those cases, a new malware filter should be created to inform VIPs when email content was blocked.
SPAM Filter
The SPAM filter provides a lot of options to determine if an email message should be marked as SPAM. Before diving into the options, it is important to understand the system Microsoft uses to mark an email message as SPAM.
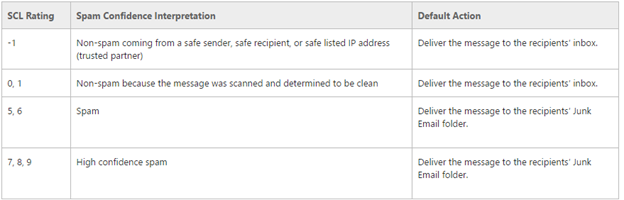
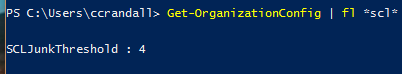
An email message goes through several stages to determine the Sender Confidence Level (SCL) score. The SCL score is made up of sender, sending domain, sending IP address, attachment type, content of the email message, all of which will impact the SCL score. By default, Microsoft uses the SCL score of 4 to determine if an email message is considered SPAM. The lower the score, the less likely the email message is considered SPAM.
To see the SCLJunkThreshold use the Get-OrganizationConfig command
Bulk Email Messages
Background information pertaining to bulk email can be found in this article; Bulk email, also referred to as graymail, is a type of email message that is more difficult to classify. Whereas junk email is a constant threat, bulk email is typically comprised of an advertisement or marketing message that’s not likely to get sent repeatedly. Bulk email is wanted by some users, and in fact, users may have deliberately signed up to receive these messages. Other users, however, may consider these types of messages to be spam. For example, some users want to receive advertising emails from the Contoso Corporation or invitations to an upcoming conference on cyber security, while others consider such emails to be spam.
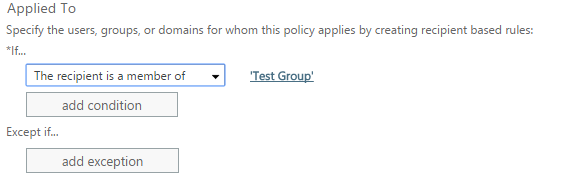
From departments like marketing, bulk email is a necessity. If bulk email is a necessity for your organization, additional transport rules could be introduced allowing email messages to members of a particular group or sender to bypass the standard SPAM engine. This would allow your organization to lower the SCL score for bulk email messages to specific recipients or senders, while enabling the bulk email message feature for all other users.
More information on transport rules can be found here.
Block List
The block list prevents email messages from specific senders or domains. My recommendation is to export the blocked senders and domains from the existing SPAM solution and import them into Office 365. You can import blocked senders and domains using PowerShell. Directions can be found in this article.
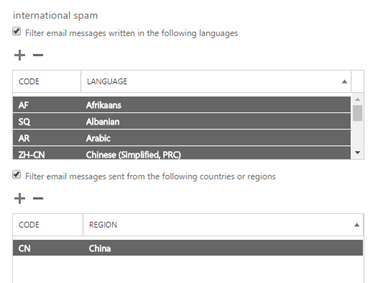
International SPAM
Background information regarding international spam can be found in this article. International SPAM can filter email messages written in specific languages, or sent from specific countries or regions. You can configure up to 86 different languages and 250 different regions. The service will apply the configured action for high confidence spam.
I recommend enabling this service for any country your company does not do business with. For larger organizations, this is not an option.
Advance Options
Background information regarding Advance Options can be found in this article. Advanced spam filtering (ASF) options give administrators the ability to inspect the various content attributes of a message. The presence of these attributes in a message either increase the spam score of the message (thereby increasing the potential for it to be identified as spam) or marks the message as spam. ASF options target specific message properties, including HTML tags and URL redirection, which are commonly found in spam messages.
Although I don’t cover all advanced options since the article above does that, I will touch on a couple of them.
| Feature | Notes |
| Image links to remote sites | |
| Numeric IP address in URL | |
| URL redirect to other port | Most legitimate sites are not redirected to another port |
| URL to .biz or .info websites | |
| Empty messages | Most legitimate email messages will have at least a subject |
| JavaScript or VBScript in HTML | |
| Frame or IFrame tags in HTML | |
| Object tags in HTML | |
| Embed tags in HTML | |
| Form tags in HTML | |
| Web bugs in HTML | |
| Apply sensitive word list | I generally don’t recommend enabling this service since administrators cannot control the list of sensitive words. |
| SPF record: hard fail | I normally don’t recommend enabling this service. If you do, make sure your partners and customers have an SPF record.
If an organization is concerned about phishing, this setting should be enabled. |
| Conditional Sender ID filtering: hard fail | I usually don’t recommend enabling this service. |
| NDR backscatter |
Transport Rules
Transport rules are a great option for one-off scenarios, blocking spoofing and phishing, blocking new malware, and creating white-lists that bypass spam engines. There isn’t a golden transport rule that applies to all organizations, however. Below are some resources that cover transport rules for Office 365. If questions or concerns arise after reading over the article, we can assist in creating transport rules that meet your business and technical requirements.
https://technet.microsoft.com/en-us/library/dn198251(v=exchg.150).aspx
Groups\Shared Mailboxes
In my experience, many SPAM messages are received through groups and shared mailboxes. There are, however, a couple of options to help with the amount of SPAM.
Outlook Rule
Create an Outlook rule that moves email messages to commonly used distribution groups in a subfolder under the Inbox folder. An Outlook rule will not stop the SPAM problem, but most end-users are more accepting of getting SPAM in a subfolder rather than their inbox.
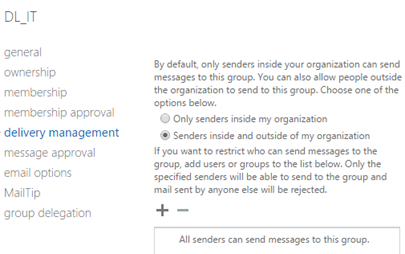
Restrict who can send to the group
Within distribution groups, under delivery management, define who can send to a group. These restrictions are commonly used to prevent unwanted email messages from being delivered to members of a given group. The downside here is that a contact is needed for all external senders that will be sending to this group.
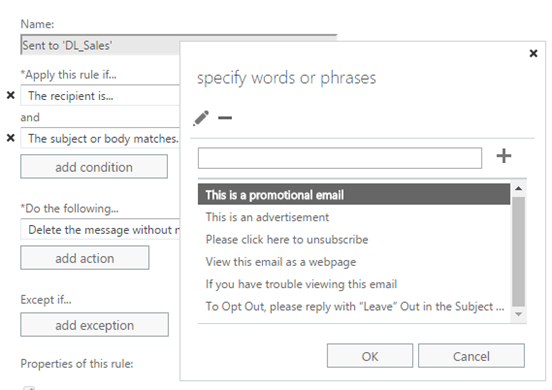
Transport Rule
A transport rule can block commonly used terms in marketing or spam email messages.
Note: This rule would be applied to the members of the group and not the group itself.
Junk folder
End-users should be using their junk folders to mark email messages as SPAM.
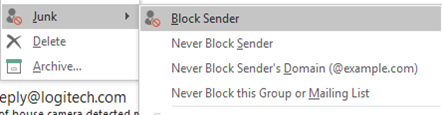
When an end-user marks an email as SPAM, the blocked sender is stored in the BlockedSendersAndDomains attribute of the mailbox. This will enable you to build a blocked sender list from all users.
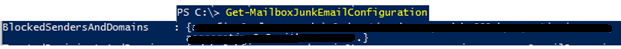
Using a PowerShell script, export the BlockedSendersAndDomains for all users, and add the senders stored in the BlockedSendersAndDomains attribute, to the blocked users in the block list under SPAM filtering.
